OCTOBER 6, 2022

There is a new malware making rounds, that targets Microsoft SQL servers, and is capable of running programs, snooping in on data, brute-forcing its way into other SQL servers, and dozens of other dangerous things.
The malware, discovered by cybersecurity analysts from DSCO CyTec, was dubbed Maggie. Maggie is distributed by pretending to be an Extended Stored Procedure DLL, a file digitally signed by an alleged South Korean company called DEEPSoft.
Usually, Extended Stored Procedure files extend SQL query functionalities via an API that accepts remote user agreements and works with unstructured data. In Maggie’s case, this functionality is abused to allow threat actors a total of 51 different commands, some of which we already mentioned.
Asian countries targeted
Maggie itself is controlled through SQL queries, that tell it which commands to execute, and which files to use.
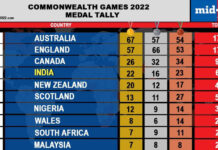
According to the researchers, the malware already infected hundreds of endpoints all over the world, most of which are located in South Korea, India, Vietnam, China, Russia, Thailand, Germany, and the United States.
Knowing the fact that Maggie attacks Microsoft SQL servers and that it has an extensive list of features, it’s safe to assume it was built as a corporate espionage tool. However, researchers were not able to determine who the threat actors behind Maggie are, where they operate from, who they’re targeting, how they succeeded in landing the malware on these servers, and to what goal.
“In order to install Maggie, an attacker has to be able to place an ESP file in a directory accessible by the MSSQL server, and has to have valid credentials to load the Maggie ESP into the server,” the researchers explained. “It is unclear how an actual attack with Maggie is performed in the real-world.”
The full list of so-far identified commands can be found on this link.
- These are the best endpoint protection services around